Academics
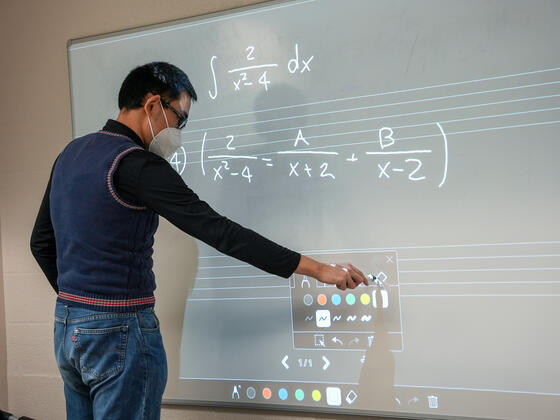
McDaniel College offers top-ranked academic programs emphasizing a liberal arts education. Our approach helps you cultivate critical thinking and the adaptability needed to thrive in any career field. With our supportive community, you'll develop the skills for success wherever life takes you.

Degrees & Programs Find the Right Program
Browse programs by:

Your Opportunities, Your Education Special Academic Opportunities

The Honors Program at McDaniel College Challenge Yourself
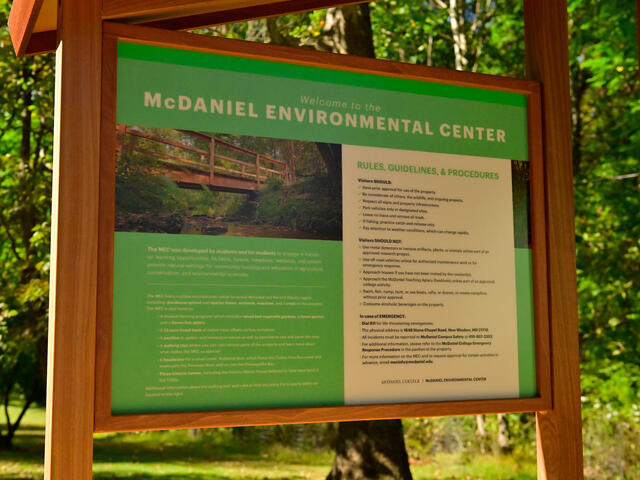
McDaniel Environmental Center Greener | More sustainable | A better place for all


Career Services, Internships & Volunteer Opportunities The Center for Experience & Opportunity